In this article, we look at some of the biggest breaches in information exposure. Blue-Pencil helps clients across Ontario safeguard information and protect their reputation with stakeholders. Click here for a free information security audit. Read along as we walk through the need to consider better records management to help prevent costly information breaches that could mean a loss of 26% of your business.
 Measuring the Costs of an Information Leak
Measuring the Costs of an Information Leak
Within all organizations, there are a number of satisfied and unsatisfied customers. For the segment of customers that are still to be convinced whether they should stay with a particular service or product, a major leaked information scandal may cause them to jump ship and switch to a competitor. This is damaging to your team in the outcome of lost profits or stakeholder support. The American Customer Satisfaction Index measures a key customer metrics across industry, brand, and sector. According to data available for 2016, 74% is the average customer satisfaction index. That would imply then that 26% of customers may be considering another service or product, which means a scandal for an organization bringing in $1M/year could result in $260,000 of lost revenue and further losses incurred to recover market position or brand image. Typically these issues are avoidable if records management is a continued focus for organizations. Blue-Pencil knows the dangers of poor records management and has experience helping customers turn their records into assets rather than liabilities.
Information Leaks that Make you Reconsider your Records Management Practices
The following are 5 examples of corporate information leaks on a major scale:
Target – Failure to Act on Security Alerts Resulted in $240M lost (Breached: 2013)
What Went Wrong: Hackers took aim at Target by installing malware on a company server as well as rigging credit card machines to steal customer information. Yet despite a sophisticated monitoring system that would have detected the intrusion and information exit from Target servers, the security alert was not actioned.
Featured Tip: Target had a million plus dollar system in place yet still failed to take action. Detection alone is not an effective security measure. Mock intrusion scenarios that involve monitoring and operations teams must be in place to ensure a million dollar system actually makes a difference rather than being an expensive noise maker. Having the right process in place is a fundamental ingredient to effective records management.
Source: http://www.bloomberg.com/news/articles/2014-03-13/target-missed-warnings-in-epic-hack-of-credit-card-data
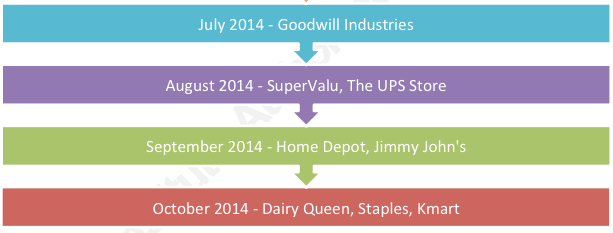
Home Depot – Vendor Security Issues Lead to Breach that Costed $62M (Breached: 2014)
What Went Wrong: Hackers used vulnerabilities in third-party vendor technology systems to eventually get access to the Home Deport systems. Once inside, malware was installed to catch customer credit card and email information.
Featured Tip: When sourcing or partnering with third-party vendors, ensure that you know what security measures they are taking and identify the integration points between your organization’s systems and theirs. If required, audit the credential and access process in place for your partners as well. Information security and end-to-end controls help organizations secure their records.
Source: https://www.sans.org/reading-room/whitepapers/breaches/case-study-home-depot-data-breach-36367
Kaspersky – Falls Prey to Human Error Leading to Compromised Security of Customers (Breached: 2011)
What went wrong: An employee was a victim of spear phishing that provided hackers with access to the security giant’s technology system. This allowed them to access key intelligence technology and data.
Featured Tip: Ensure that employees are trained on all social phishing tactics and provide technology controls to block accidental clicks on suspicious activity. In records management, the greatest asset and vulnerability is the human factor. Training, resources, and reinforcement must be in place.
Source: https://www.wired.com/2015/06/kaspersky-finds-new-nation-state-attack-network/
Residential and Commercial clients continue to make Blue-Pencil their go-to provider to help them protect against data theft. Here is what a recent customer has to say about Blue-Pencil.
“Always efficient and the process is always so easy! They come by on schedule and when we have extra shredding that needs to be done it’s never an issue! Highly recommended. The gentlemen Adam and Lenny are also super polite, friendly and professional!”
– Vanessa
Click here for more reviews.
eBay – Employee Passwords Open 140M Customer Records (Breached: 2014)
What went wrong: eBay also fell prey to a social engineering ploy that led to the exposure of customer information like name, address, phone number, and date of birth. Perpetrators commandeered a number of employee credentials to gain access to the corporate network.
Featured Tip: One of the best ways to prevent unauthorized account access is to continually change passwords. Some intrusions can last for a year or more without being detected, but having passwords managed proactively could stem on-going data loss. When paired with mechanisms to detect malware this is a simple and effective way to fight data intrusion.
Source: http://info.rippleshot.com/blog/ebay
LinkedIn – Counter Measures to Previous Leak Ineffective, Leading to 100M+ Users Compromised (Breached: 2012)
What Went Wrong: in 2012 LinkedIn had a data breach that caused it to compromise 6.5 million accounts, and in 2016 another 115 million accounts were exposed. The issue was that encrypted data was left out in public. Though a subset of accounts was exposed, LinkedIn did not take proactive measures to ensure the remaining accounts could not be cracked.
Featured Tip: Organizations must consider their competitive position not only with other organizations but with data thieves. Had LinkedIn thought of this as an on-going engagement, they would have prioritized ways of further protecting the remaining passwords that had not been compromised.
Source: https://www.grahamcluley.com/2016/05/linkedin-data-breach-haunt/
Blue-Pencil Helps Organizations Synergize Policy, Process, People, and Technology with Information Management to Deliver Value
Without a proven advisor, even the best strategies and technologies can remain disparate systems and organizations may remain at risk or suffer declining productivity. Our team focuses on helping companies ensure secure and effective records management across industries like government, healthcare, manufacturing, and small business.
Expert advisor in strategic information management and proven hands-on experience
Ability to deliver compliance while managing organizational efficiency
Proven systems and methodology for managing information retention schedules
Training, resources, and support for your staff to become adept at information management
High standards in information destruction services with NAID AAA and Privacy+ certification
Blue-Pencil is an information security company that has been serving the needs of clients in Canada since 2004. We have grown our document security business over the past 10 years, serving more than 6,000 organizations including small and medium-sized companies as well as Fortune 500 businesses. We have recently launched two new divisions: Documents Storage and Records Management division and Document Imaging and Scanning Solutions division. This allows us to offer full spectrum, comprehensive solutions for information security management. We service the GTA and surrounding cities – click here for a full list of our service areas. If you’d like to learn more about us and what we can do for you, contact us today!
Sources:
https://securityintelligence.com/the-top-5-retail-breaches/
 Measuring the Costs of an Information Leak
Measuring the Costs of an Information Leak